PC Guard Software Protection System
Professional software copy protection and licensing system for .NET Framework, Windows .NET Core (x86/x64), Windows .NET and native Windows 32bit and 64bit applications.
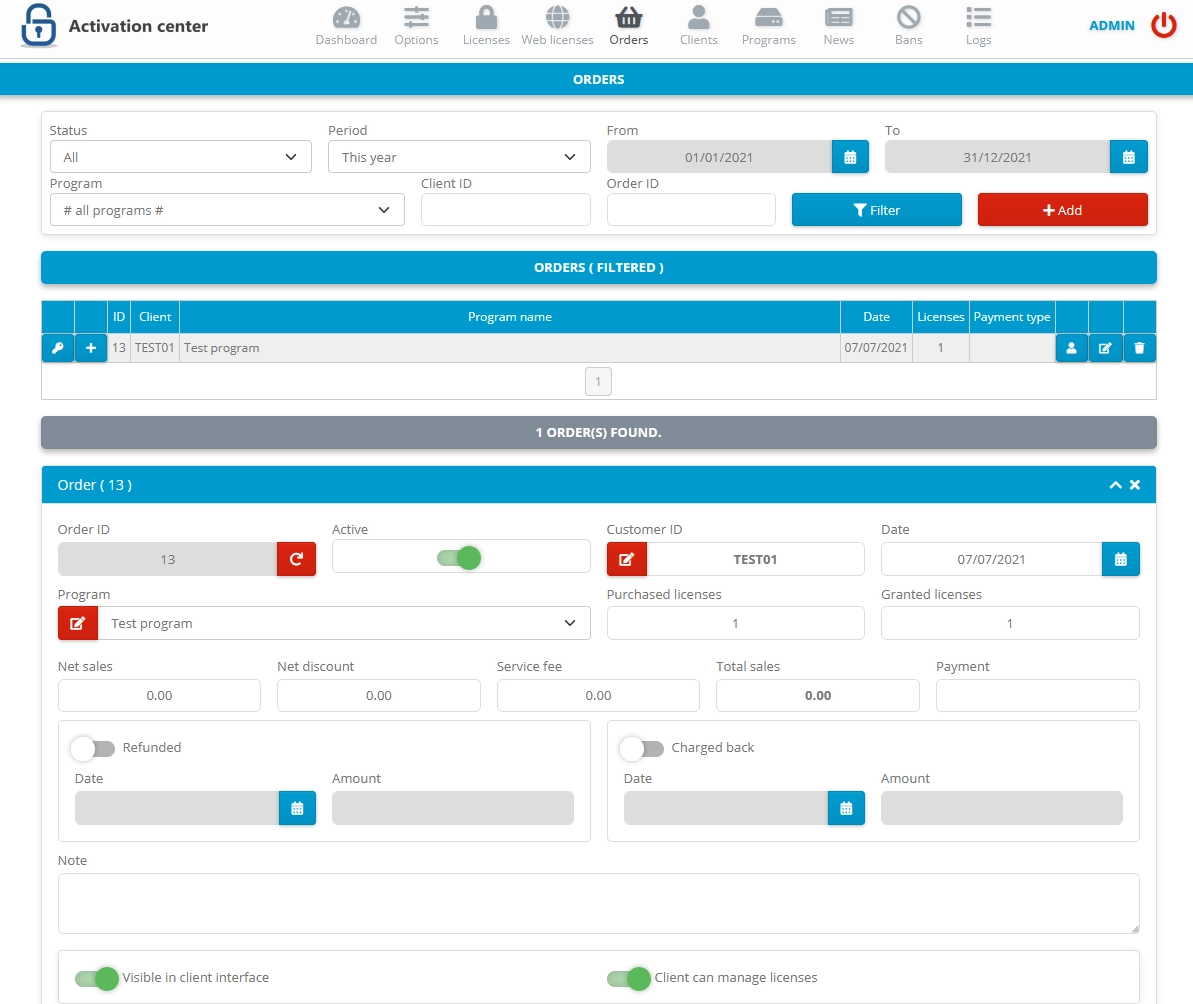
Activation center
Ready-made, full featured ASP .NET web application for management of Clients, Programs, Orders and Licenses with flexible automated activation system for programs protected with PC Guard family products.
SourceArmor .NET
Protect your code from prying eyes with professional obfuscation system for .NET framework applications.
SourceArmor obfuscator will transform your application, by applying obfuscating transformations and by keeping its functionally identical but in the same time much more difficult to reverse engineer.
This includes overloaded renaming of types, methods, events, properties, parameters, fields and events, resources, encryption of strings, control flow obfuscation, metadata pruning, insertion of invalid IL instructions, suppression of disassemblers and many other techniques.